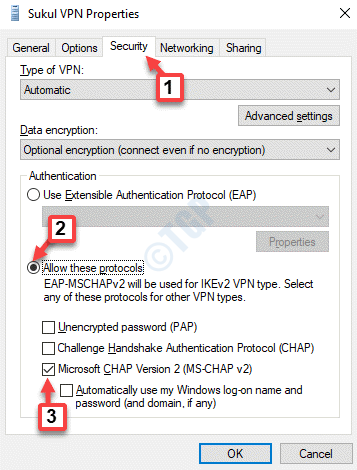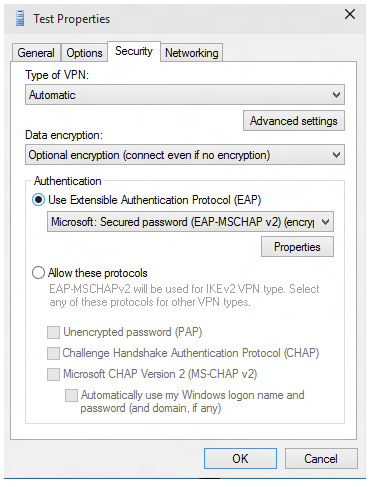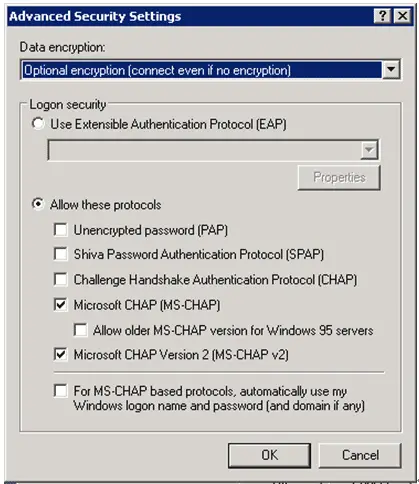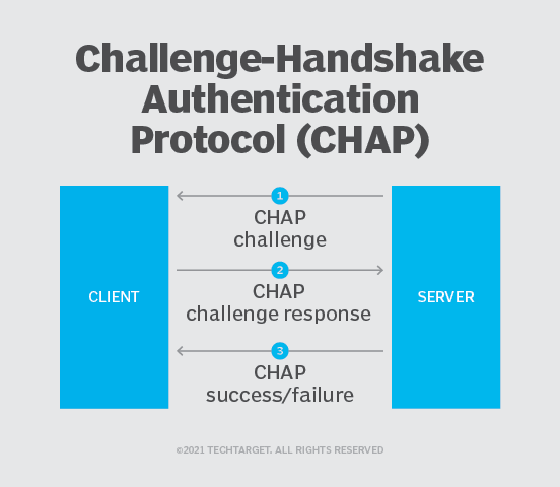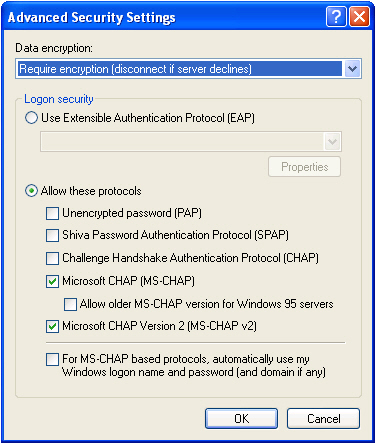
Step 3: Configure MS-CHAP on the Client | CompTIA Network+ Video Mentor: Configuring an L2TP-Based VPN | Pearson IT Certification
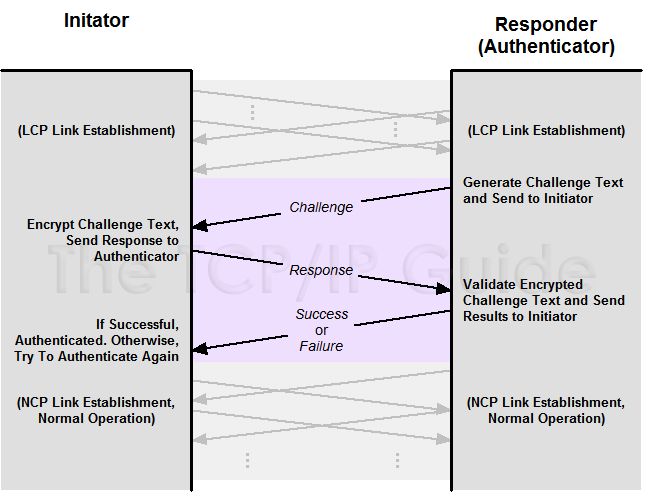
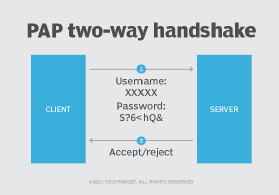
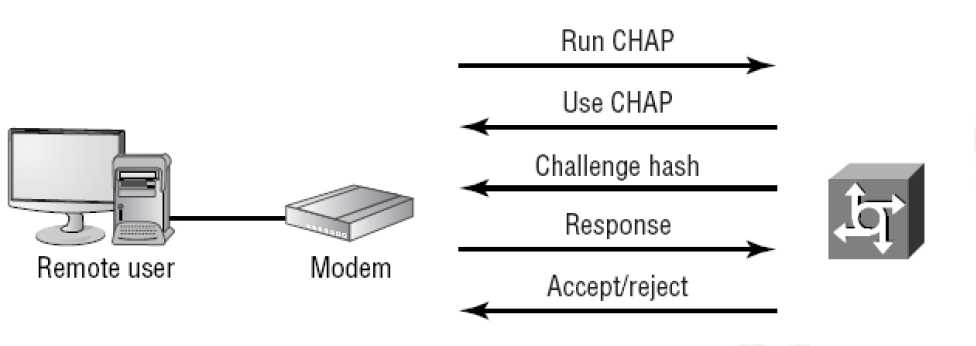
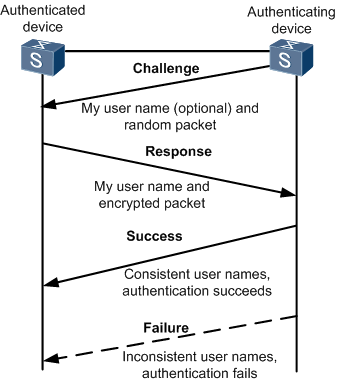
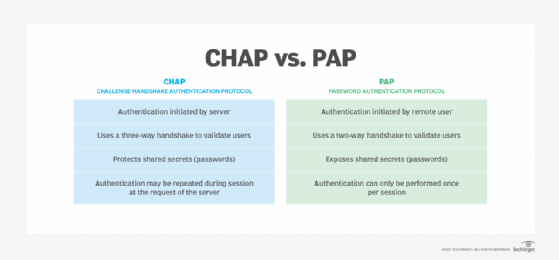
The TCP/IP Guide - PPP Authentication Protocols: Password Authentication Protocol (PAP) and Challenge Handshake Authentication Protocol (CHAP)
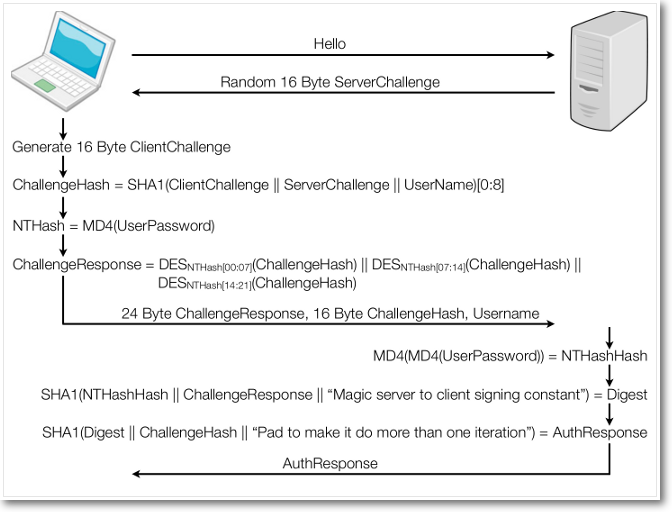
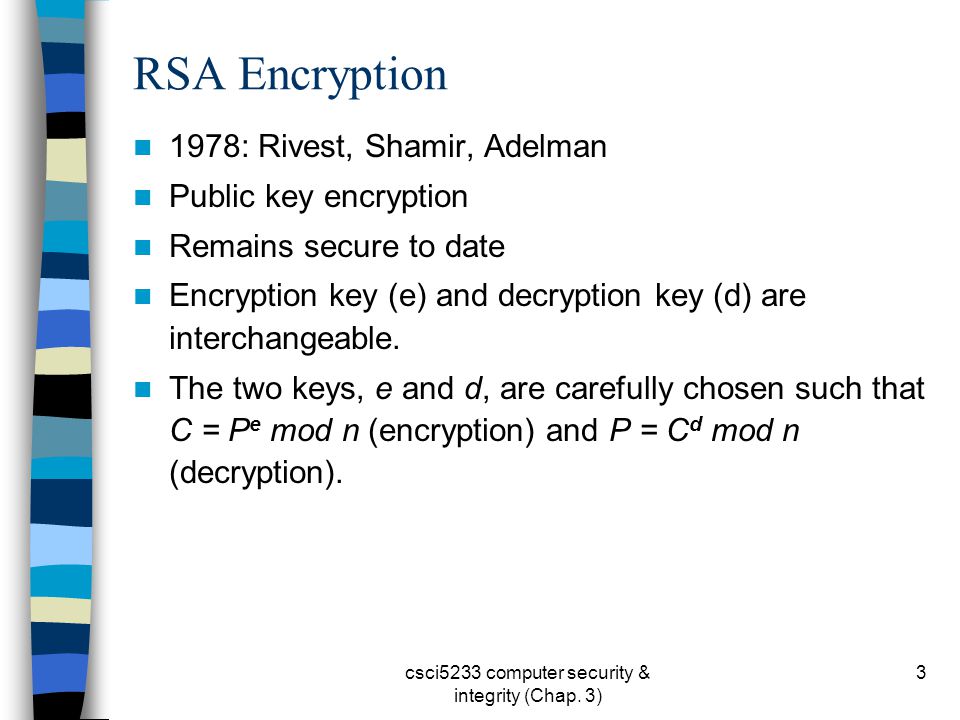
Authentication and Identity Protocols :: Chapter 2. Basic Security Mechanics and Mechanisms :: Wireless lan security :: Networking :: eTutorials.org