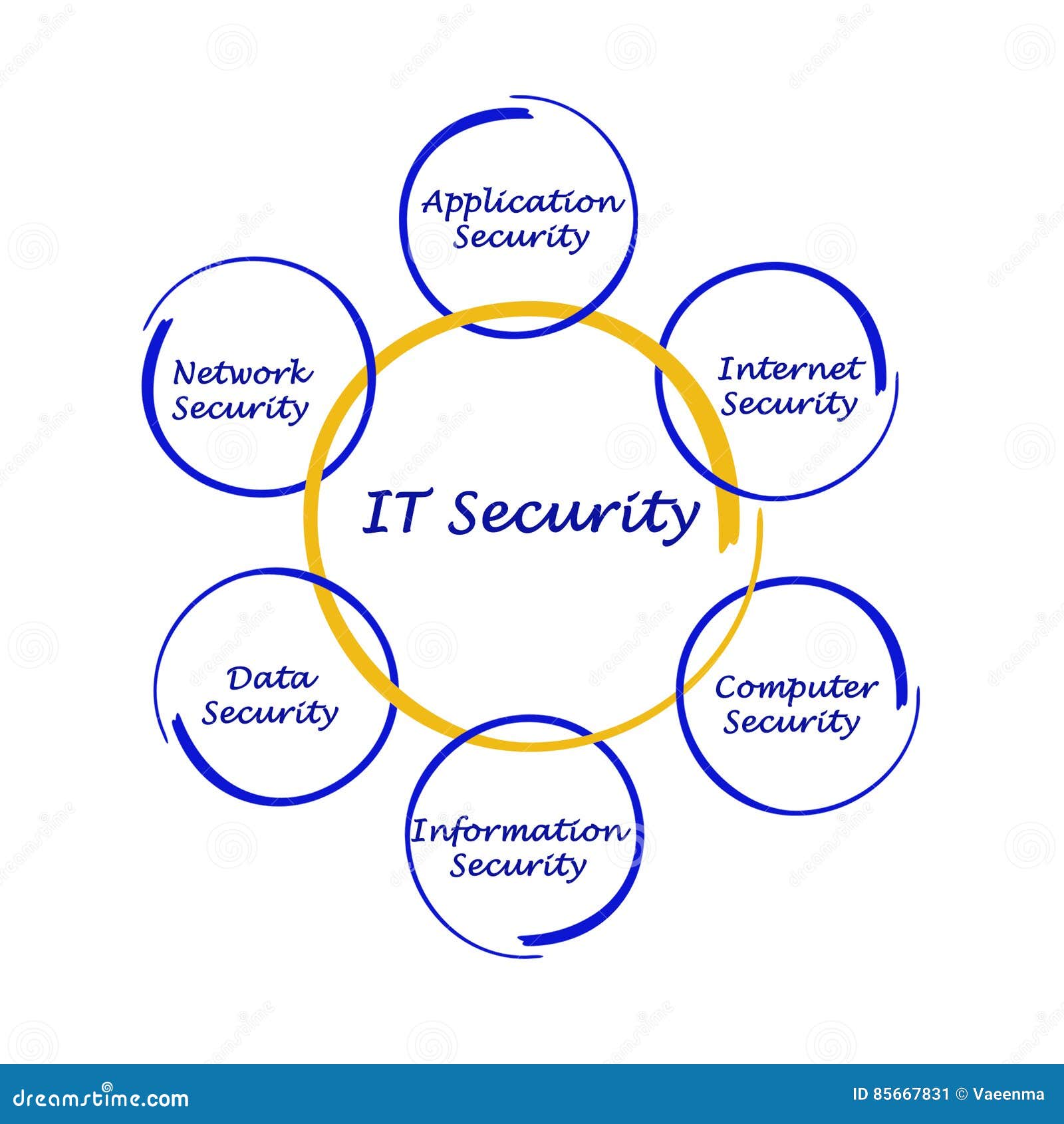
Cyber Security Feed on Twitter: "RT @iExperts10: Network Security, System Security, Cyber Security, Information Security 🔒🔐 #cybersecurity #cybersecurityawareness #informa…" / Twitter

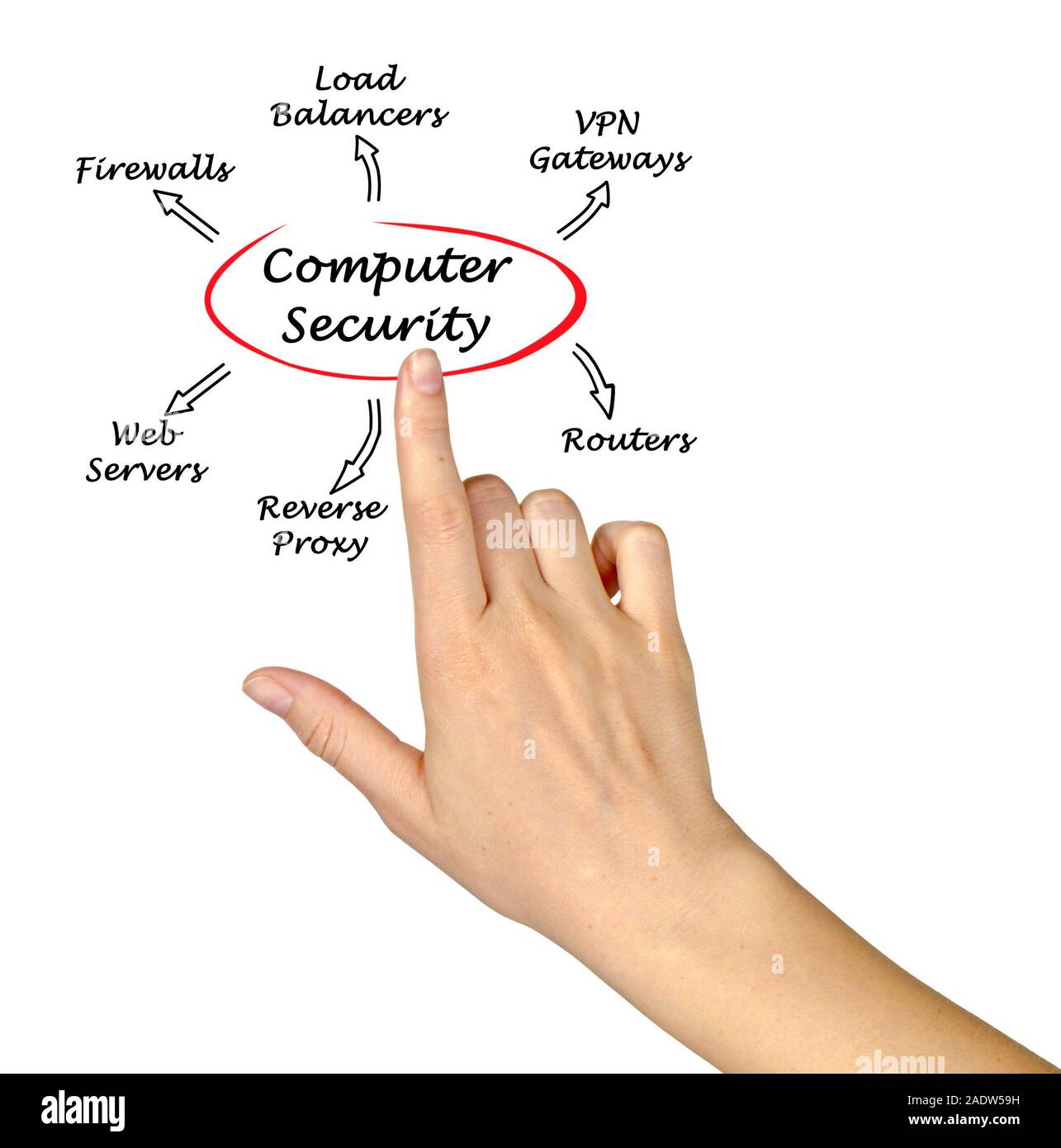
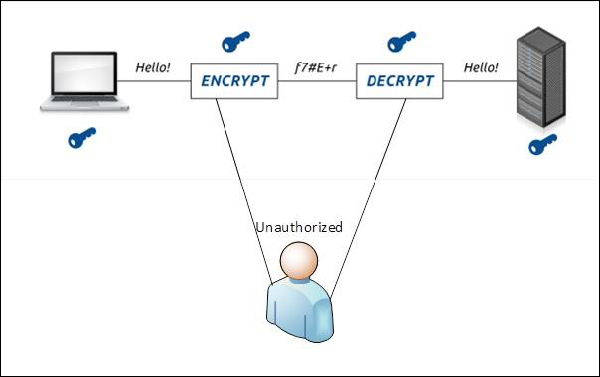
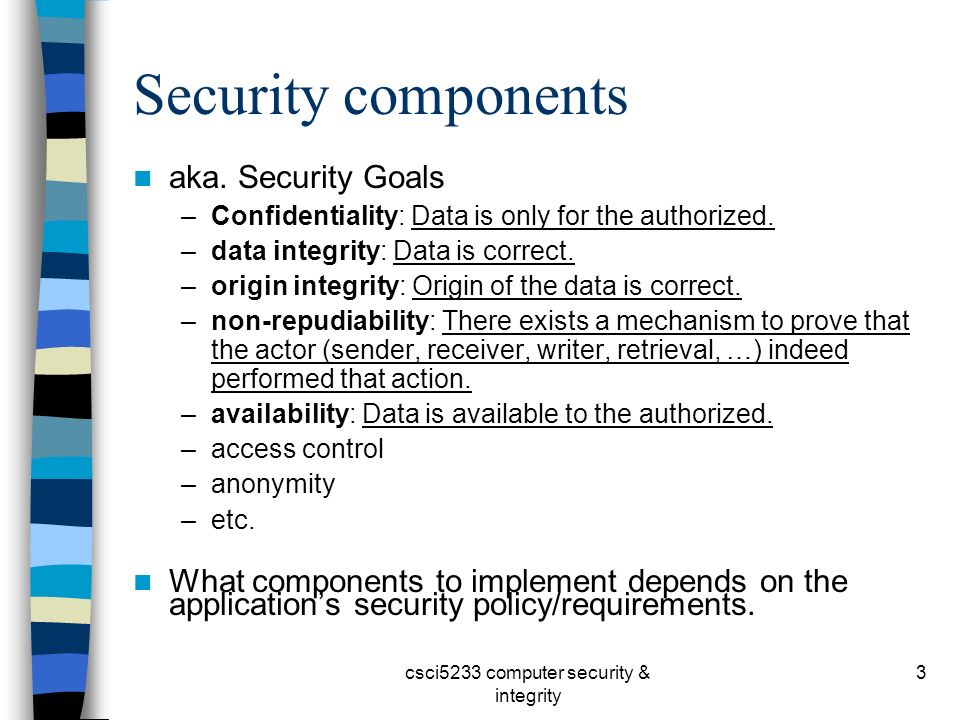
Cryptography and Computer Security: The life cycle of Passwords & Keys Life cycle and their relationship with your protection