What is Computer Hacking? - Definition, Prevention & History - Video & Lesson Transcript | Study.com

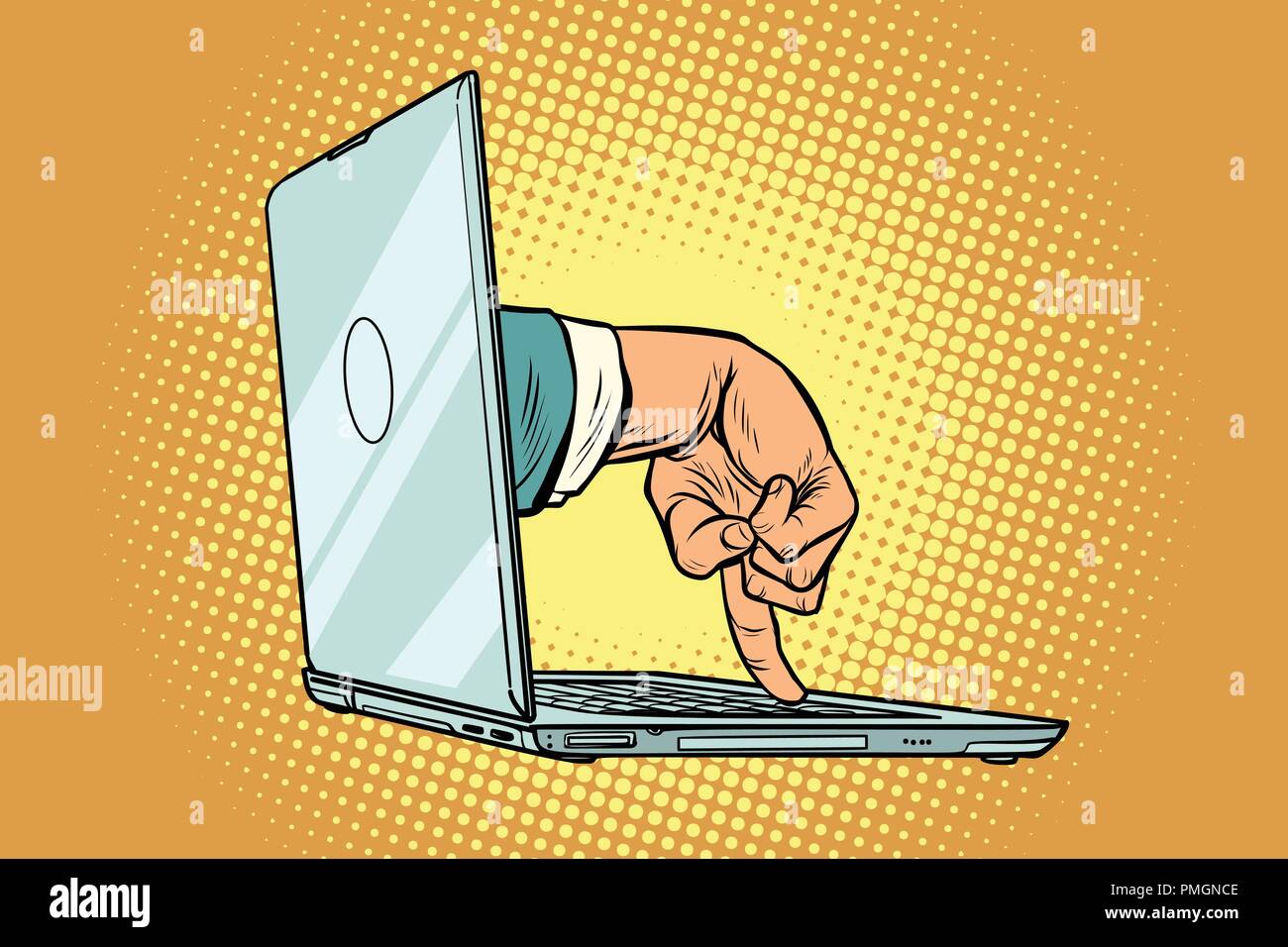
Computer Intrusion Detection and Network Monitoring: A Statistical Viewpoint (Information Science and Statistics): Marchette, David J.: 9780387952819: Amazon.com: Books

Worried that quantum computers will supercharge hacking, White House calls for encryption shift | Science | AAAS