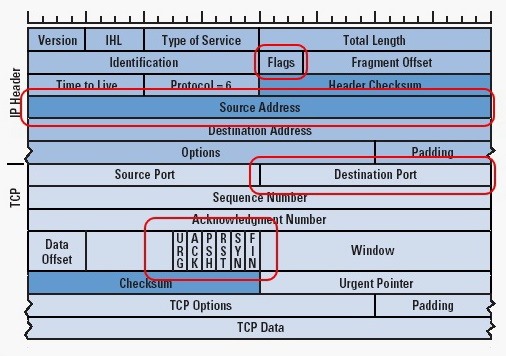
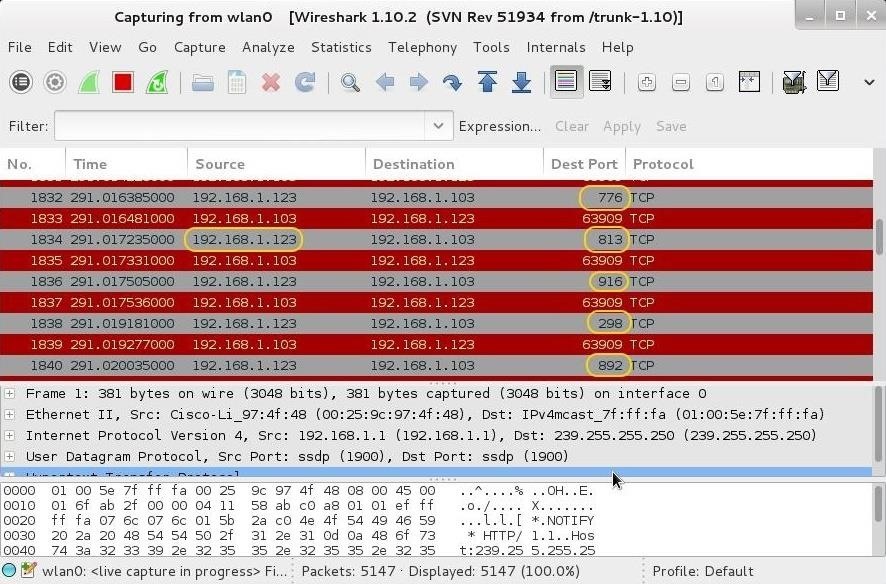
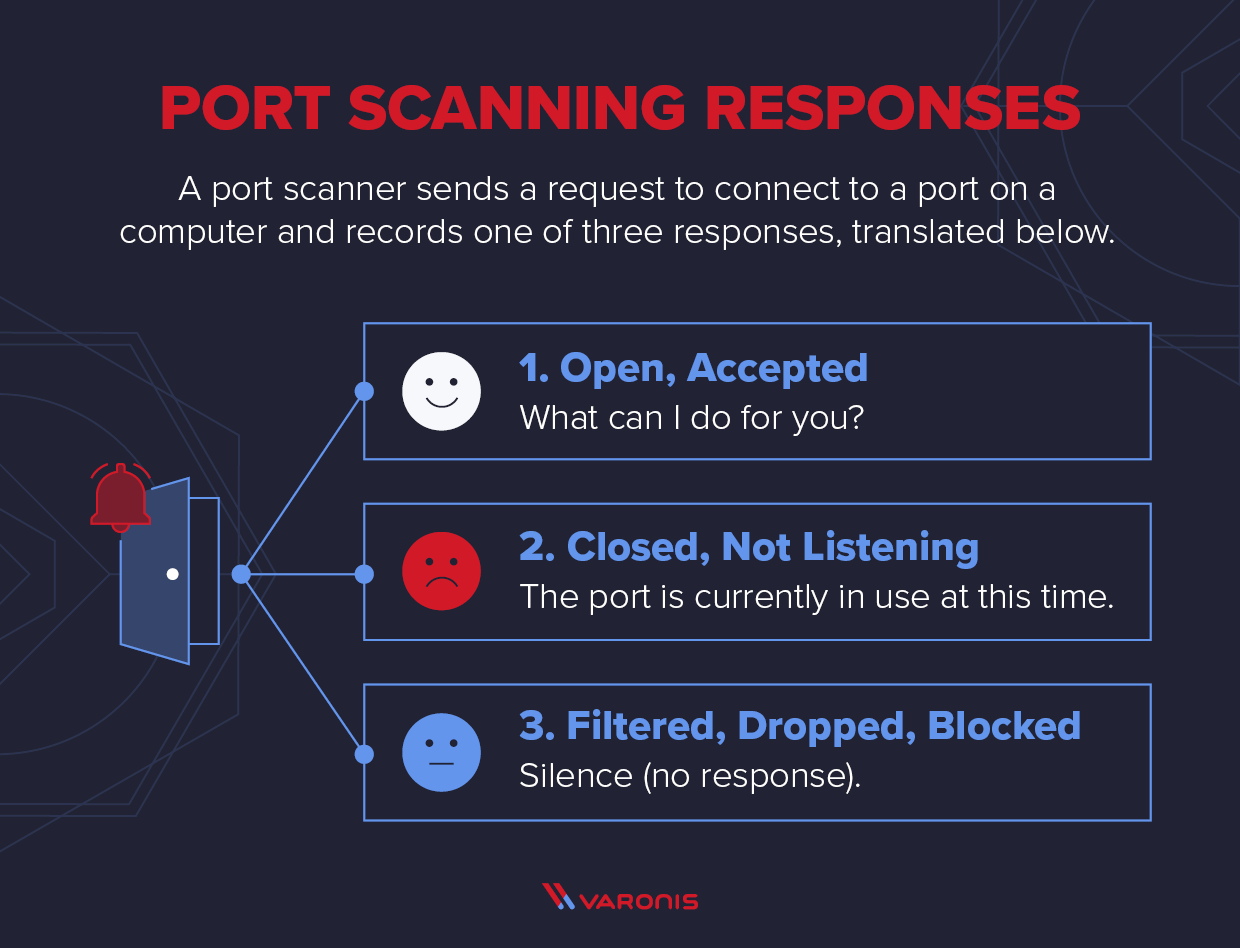
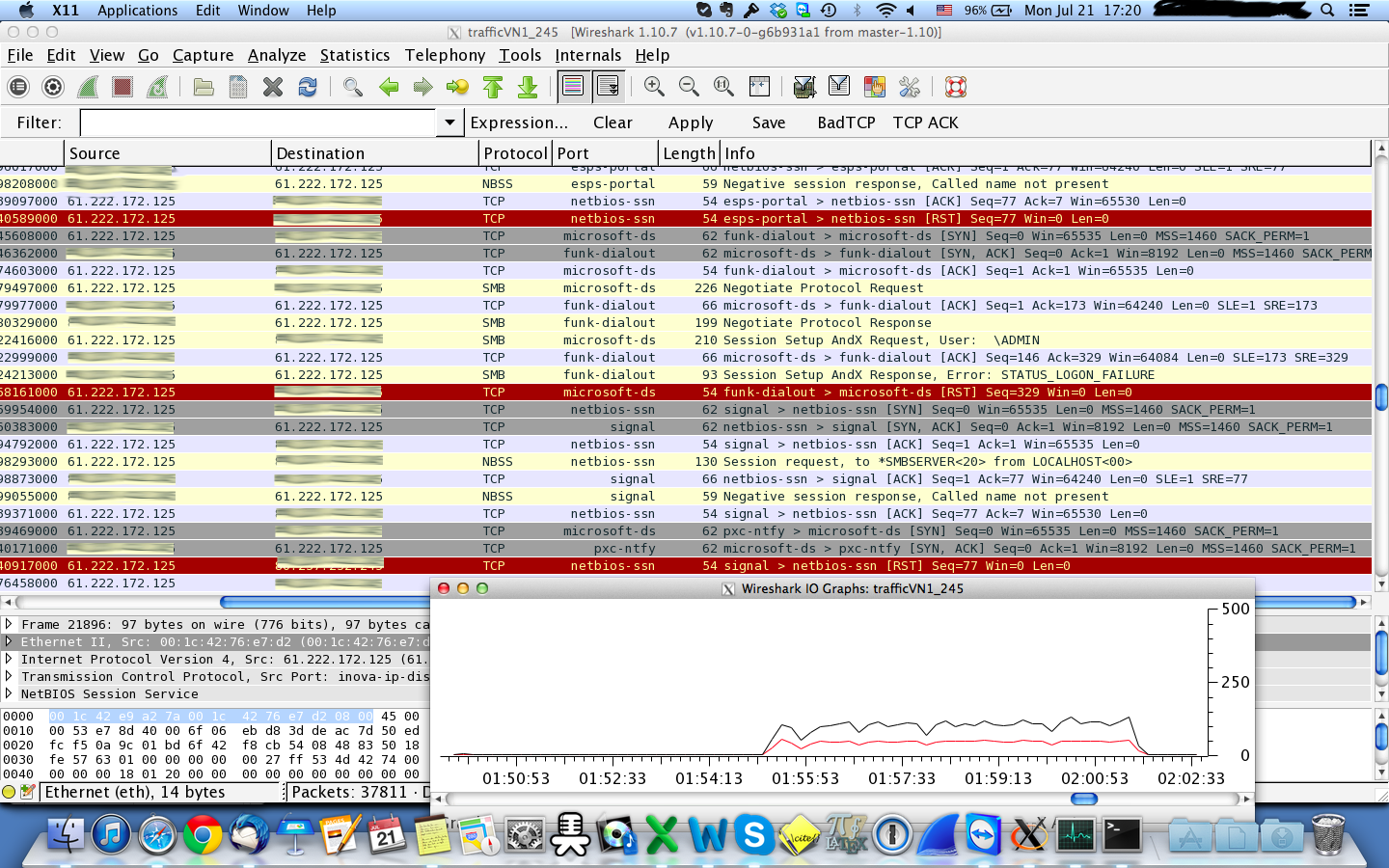
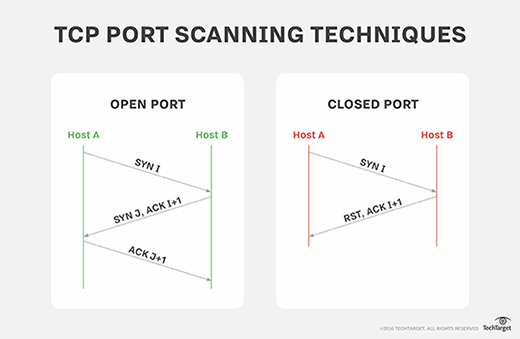
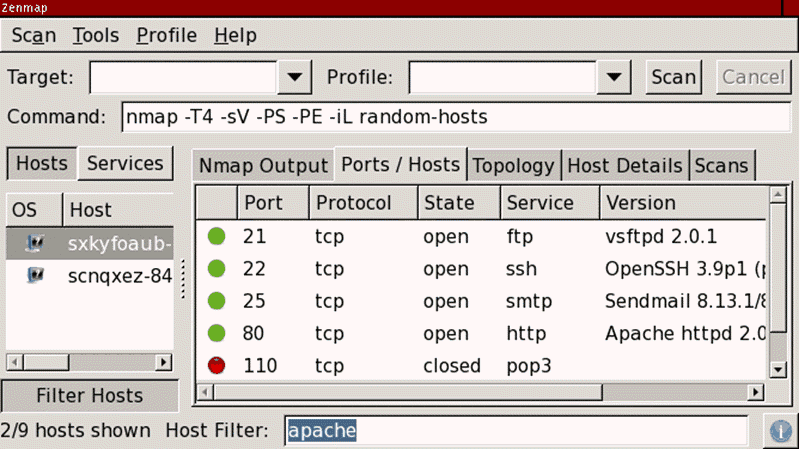
Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 10 (Identifying Signatures of a Port Scan & DoS Attack) « Null Byte :: WonderHowTo
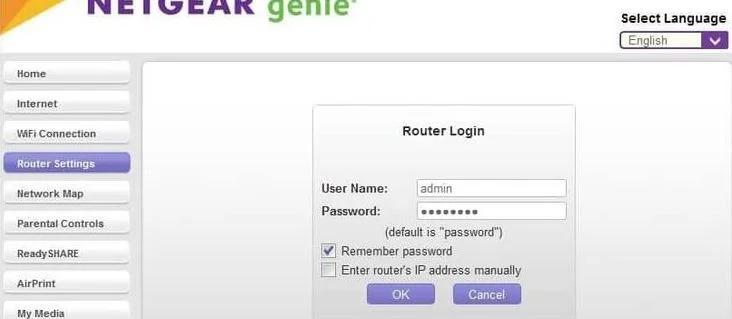
TCP SYN Flood Attack - Router IP - ESET Internet Security & ESET Smart Security Premium - ESET Security Forum

Grayscale images of DoS (a), DDoS (b), PortScan (c), FTP-Patator (d),... | Download Scientific Diagram

Hack Like a Pro: Digital Forensics for the Aspiring Hacker, Part 10 (Identifying Signatures of a Port Scan & DoS Attack) « Null Byte :: WonderHowTo

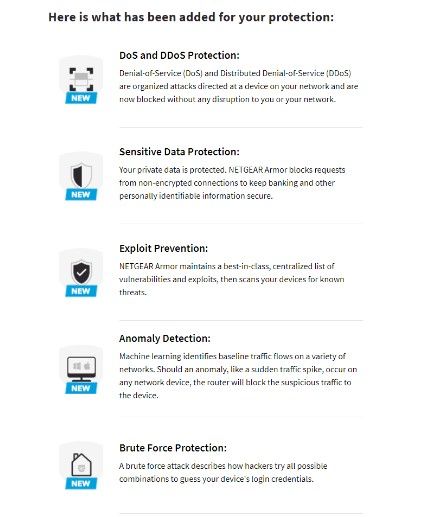


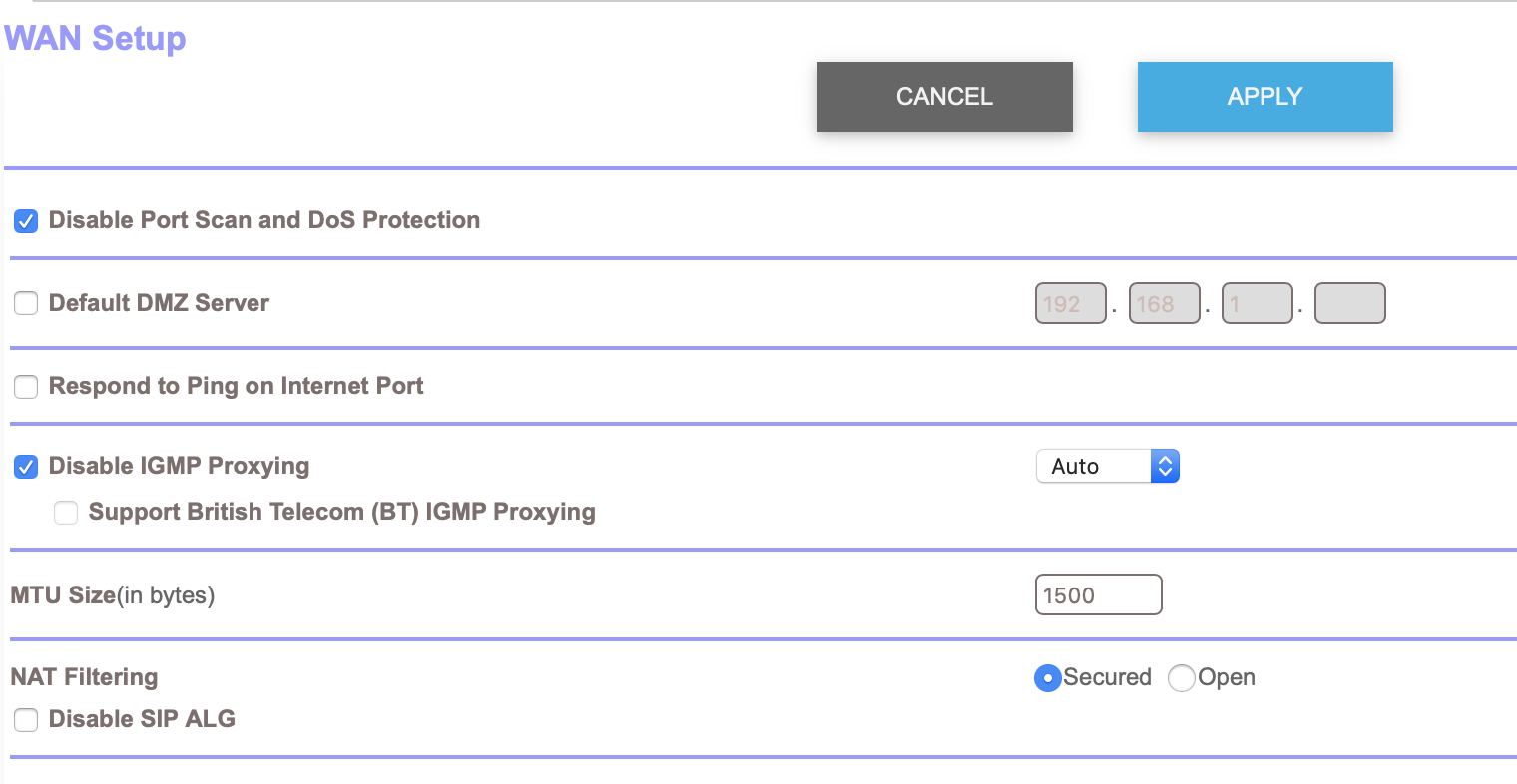

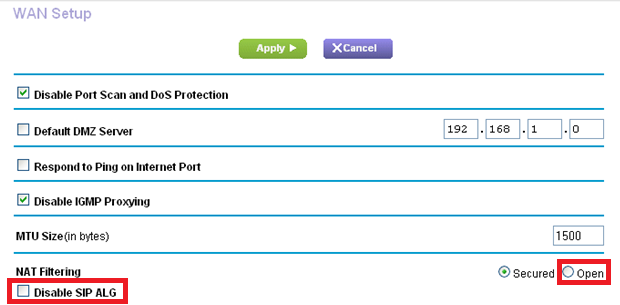
![PSA] Disabling features in my Routers Firewall cleared up 80% of my hitching : r/Planetside PSA] Disabling features in my Routers Firewall cleared up 80% of my hitching : r/Planetside](http://i.gyazo.com/9de97725717d0828967413e4ec035916.png)