Trusted Path and Trusted Channel by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
COTS-Based Trusted Computing: Getting Started in Next-Generation Mission-Critical Electronics | Curtiss-Wright Defense Solutions
CISSP PRACTICE QUESTIONS – 20190822 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu






![PDF] Trusted computing for infrastructure | Semantic Scholar PDF] Trusted computing for infrastructure | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/ac08dbc542a115a6ce39919f8508985d5728d8bf/6-Figure4-1.png)
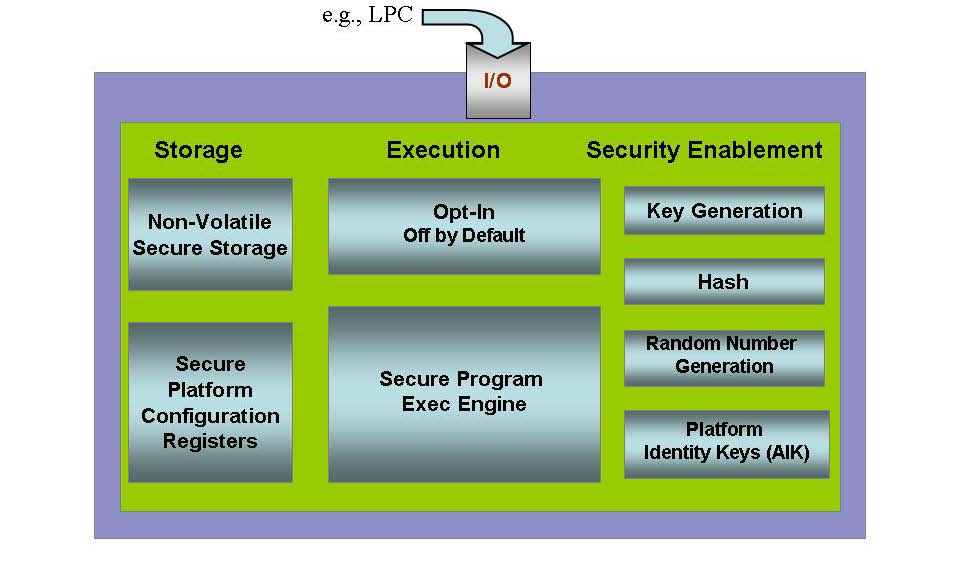





![PDF] Trusted Computing Platforms , the Next Security Solution | Semantic Scholar PDF] Trusted Computing Platforms , the Next Security Solution | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4a82f9c66e39b1335bdc8fa3eb0880e9a0370446/12-Figure5-1.png)